Deep Security Features
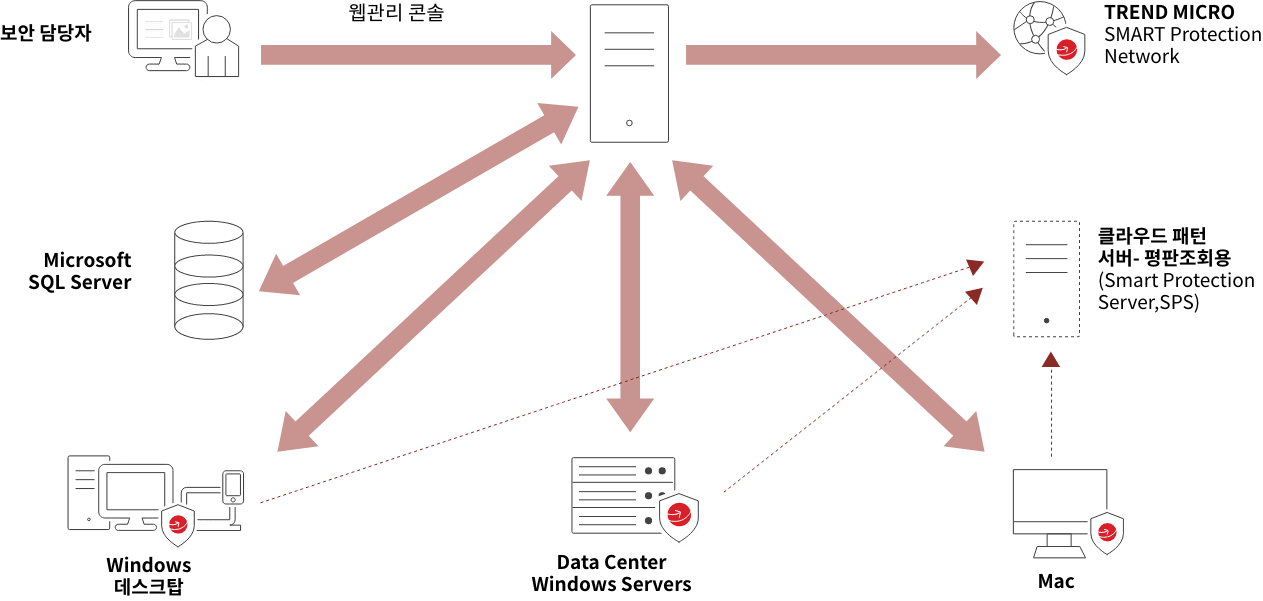
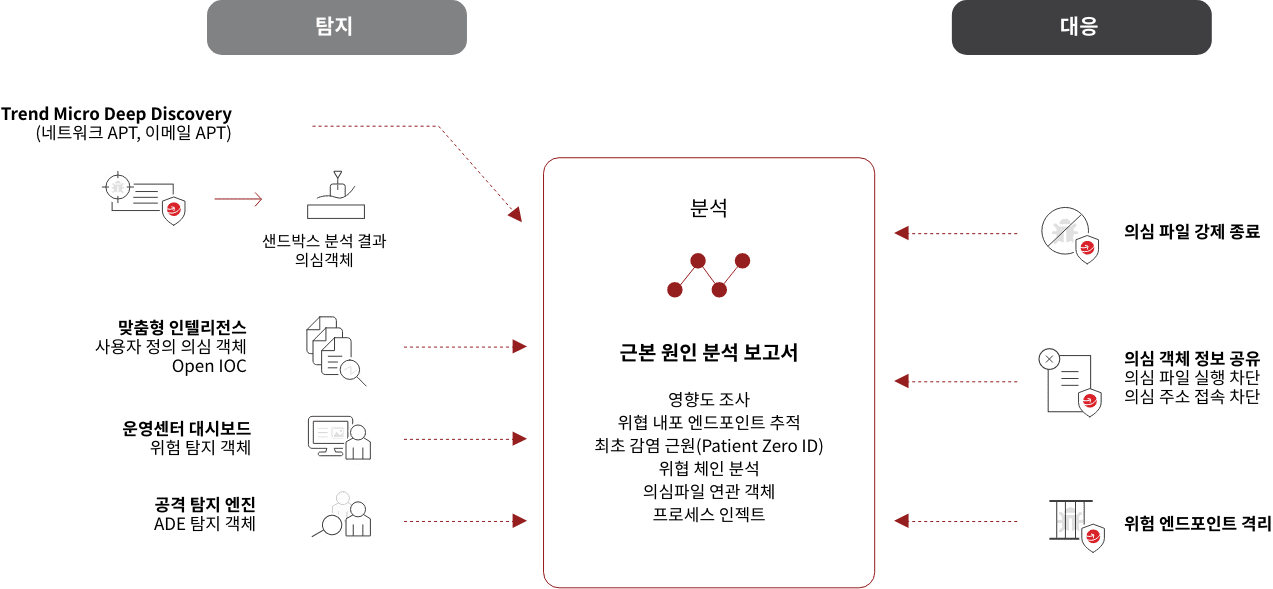
- Host-Based Integrated Security
- Docker + Container Environment Security
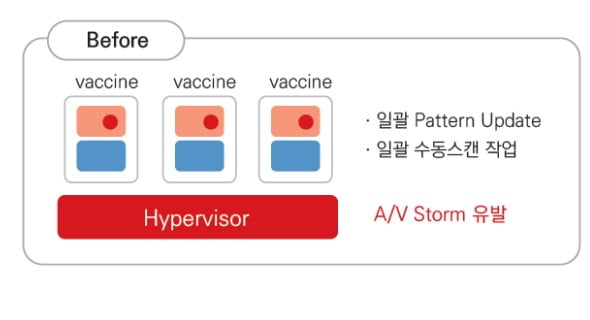
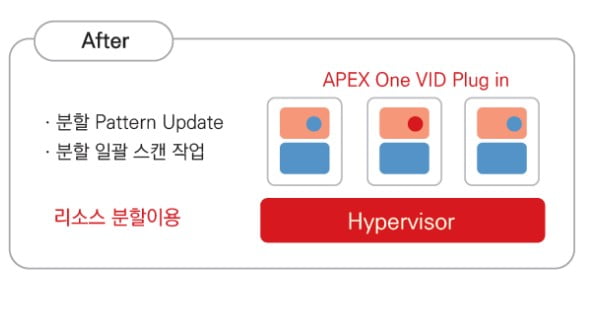
- Private Cloud, Data Center-Optimized Security Solutions
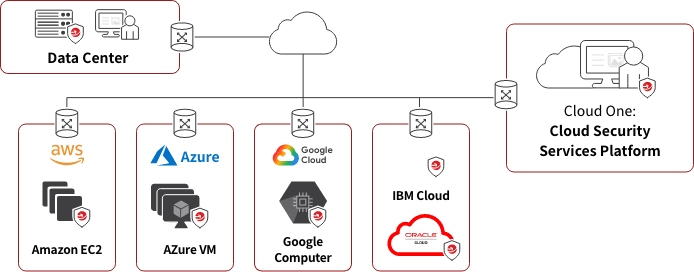
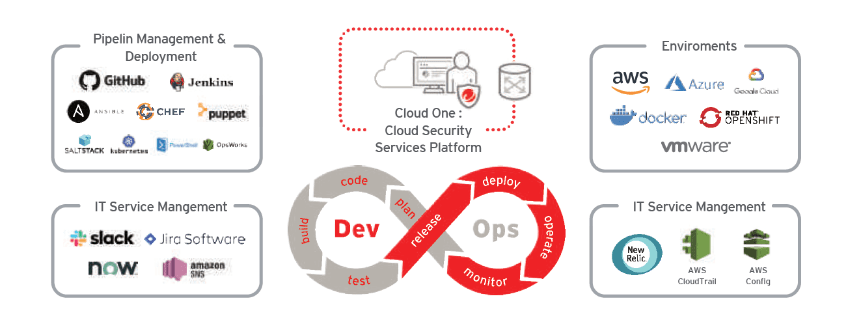
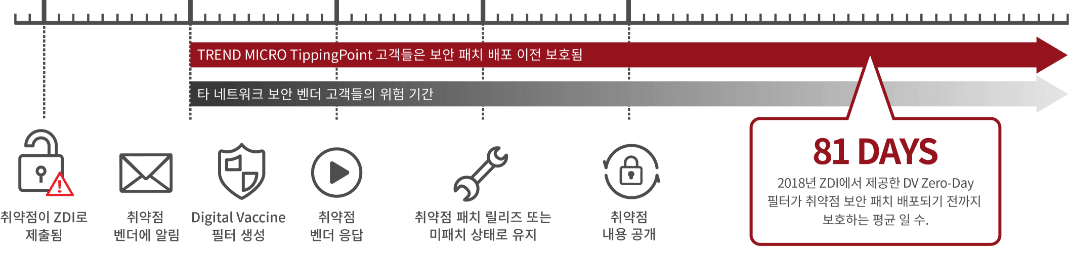
- Multi-hybrid cloud security integration
- Provides host-based security for cloud environments
- Hybrid cloud security integration (cloud, virtualization, physical) management
- Most platform support (Linux, Windows, Unix)
- Meet key security compliance (PCI-DDS, HIPPA, H국제CC 최고등급, EAL2+ITECH)
- CC certification, GS certification
- Nara Market (Procurement) Registration
- The nation's largest data center customer's choice of security solution
- International CC Highest Rating, EAL2+