Cyber Security Consulting
Information protection consulting provides an information protection master plan by identifying
potential risks (access, loss of information, forgery, tampering, etc.) during the creation,
processing, storage, and deletion of information assets to improve the level of information protection.
potential risks (access, loss of information, forgery, tampering, etc.) during the creation,
processing, storage, and deletion of information assets to improve the level of information protection.
Inspection of the information management status of online investment-linked financial industry
In accordance with Article 30(2) of the Online Investment-linked Financial Business Act, an online
investment-linked financial business entity shall check the status of online information management
at least once a year, report the results to the Financial Services Commission within three months,
and entrust the inspection to a specialized institution such as an information protection service company.
Information Protection Preliminary Inspection System
Information and communication services or telecommunication businesses under Article 45(2)
of the Information and Communication Network Act shall check security-related matters
(written inspection, on-site inspection, or remote inspection) when they intend to establish
a new information and communication network or provide information and communication services.
Features
Comprehensive, continuous and balanced management is required through systematic response by establishing
countermeasures for each security threat and establishing a management system to avoid bias.
countermeasures for each security threat and establishing a management system to avoid bias.
-
Independent Information
Protection Management
System Application of BOSSᵐ,
a methodology for establishment -
Establishing an information protection
system tailored to the capabilities of each organization -
Present specific information
protection master plans -
Recommend a living information
protection solution that
reflects the latest security trends
Goals
Comprehensive, continuous and balanced management is required through systematic response by establishing
countermeasures for each security threat and establishing a management system to avoid bias.
countermeasures for each security threat and establishing a management system to avoid bias.

- Identify and analyze their security status and issues based on data protection standards
- Identify potential threats to your organization based on your expertise in security
- Develop improvements through detailed consulting and provide an information protection master plan
- Directions to improve the level of information protection
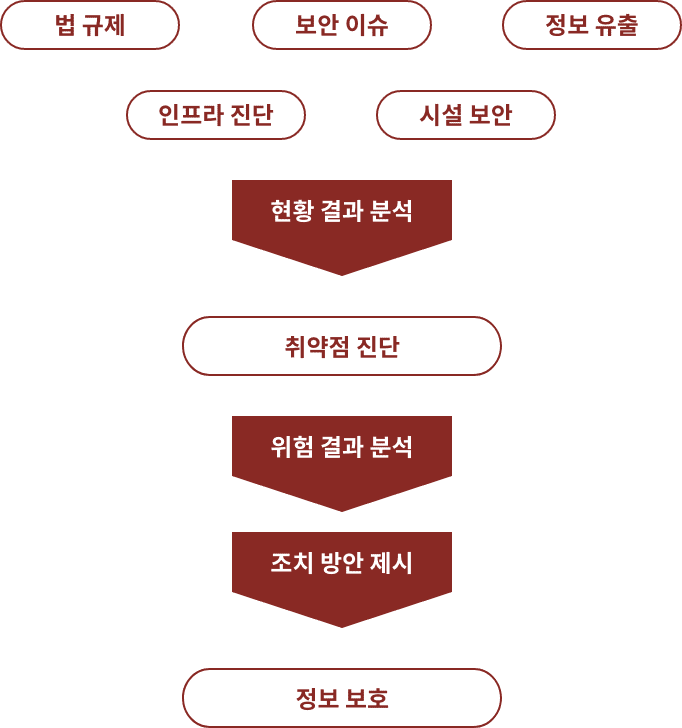
Consulting Methods
Based on BOSS IV, a methodology for establishing an information protection management system, modules suitable for each task are
combined to proceed in the order of initiation, vulnerability diagnosis, risk analysis, countermeasure establishment, and termination.
combined to proceed in the order of initiation, vulnerability diagnosis, risk analysis, countermeasure establishment, and termination.
Vulnerability Diagnostics
GAP analysis that analyzes the level of information protection is analyzed
by area through interviews with the person in charge and working-level officials,
review of information protection regulations and guidelines, and due diligence
to derive data for improving the customer's level of information protection.
Risk Analysis
Risk analysis identifies possible threats to vulnerabilities identified
during the diagnosis process and establishes remedial measures based on
the importance of assets and the degree of risk level.
Establishment of Countermeasures
Establish a master plan by prioritizing the issues derived from the risk
analysis and selecting a step-by-step roadmap according to the customer's direction.
Expectation Effectiveness
Qualitative Effect
- Comprehensive understanding of threats to information protection within your organization
- Improving corporate credibility and market competitiveness through the establishment of a comprehensive information protection system
Quantitative Effect
- Master plan, systematic budgeting and investment capabilities
- Controlling excessive spending on information protection equipment
- Mitigate legal responsibility in the event of a security incident
- Gain loyal customers who are sensitive to information protection, resulting in increased sales
- Estimate the amount of budget required to carry out the derived improvement tasks
